7 Most Critical IT Security Protections Every Business Must Have In Place Now To Protect Themselves

"Cybercrime is so widespread that it’s practically inevitable that your company – large OR small – will be attacked. However, a few small preventative measures CAN PREPARE YOU and minimize (or outright eliminate) any reputational damages, losses, litigation, embarrassment and costs."
~ Joseph Martin - President/CEO of Triangle IT Group
When You Fall Victim To A Cyber-Attack Through No Fault Of Your Own, Will They Call You Stupid…Or Just Irresponsible?
It’s EXTREMELY unfair, isn’t it? Victims of all other crimes – burglary, rape, mugging, carjacking, theft – get sympathy from others. They are called “victims,” and assistance and support come flooding in.
But if your business is the victim of a cybercrime attack where client or patient data is compromised, you will NOT get such sympathy. You will be instantly labeled as stupid or irresponsible. You will be investigated and questioned about what you did to prevent this from happening – and if the answer is not adequate, you can be found liable, facing serious fines and lawsuits.You will be required by law to tell your clients and/or patients that YOU exposed their private records, financials, and data to a criminal. Your competition will have a heyday over this, and clients will leave in droves once they discover you’ve been compromised. Your bank will NOT come to your rescue either, and unless you have a very specific type of crime insurance, any financial losses will not be covered.
Here’s The Ugly Truth:
You already know that cybercrime is a very real threat to you – but it’s very possible that you’re underestimating the potential damage, OR you are being ill-advised and underserved by the employees and/or vendors you hired to protect your business from these threats.
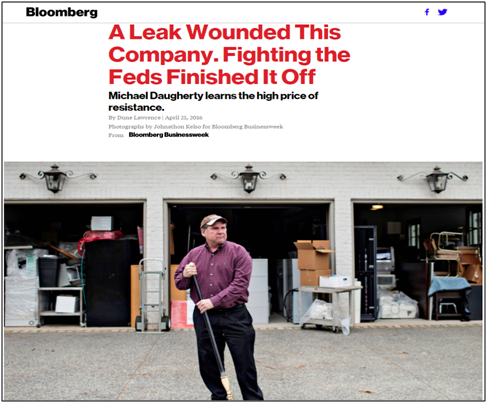
ONE cyber-attack…one slip up from even a smart, tenured employee clicking on the wrong e-mail…can open the door to ABSOLUTE FINANCIAL DEVASTATION, and undo everything you’ve worked so hard to achieve. Take the story of Michael Daugherty, former CEO of LabMD. His $4 million Atlanta-based company tested blood, urine and tissue samples for urologists – a business that was required to comply with federal rules on data privacy as outlined in the Health Insurance Portability and Accountability Act, or HIPAA.
He HAD an IT team in place that he believed was protecting them from a data breach – yet the manager of his billing department was able to download a file-sharing program to the company’s network to listen to music, and unknowingly left her documents folder (which contained over 9,000 patient files) open for sharing with other users of the peer-to-peer network. This allowed an unscrupulous organization to hack in and gain access to the file and use it against them for extortion.
When Daugherty refused to pay them for their “services,” the company reported him to the Federal Trade Commission, who then came knocking. After filing some 5,000 pages of documents to Washington, he was told the information he had shared on the situation was “inadequate,” and the FTC requested in-person testimony from the staff regarding the breach, and more details on what training manuals he had provided to his employees regarding cybersecurity, documentation on firewalls and penetration testing. (QUESTION: ARE YOU ACTUALLY DOING ANY OF THIS NOW?)
Long story short, his employees blamed HIM and left. Sales steeply declined as clients took their business elsewhere. His insurance providers refused to renew their policies. The emotional strain on him – not to mention the financial burden of having to pay attorneys – took its toll, and eventually, he closed the doors to his business, jamming medical equipment into his garage where it remains today (image below).
“Not My Company…Not My People…” You Say?
Don’t think you’re in danger because you’re “small” and not a big target like a J.P. Morgan or Home Depot? Or that you have “good” people and protections in place? Think again. Every single day, 82,000 NEW malware threats are being released, and more than HALF of the cyber-attacks occurring are aimed at small businesses; you just don’t hear about it because it’s kept quiet for fear of attracting bad PR, lawsuits and data-breach fines, and out of sheer embarrassment – but make no mistake: small businesses are being compromised daily, and the smug ignorance of “that won’t happen to me” is an absolute surefire way to leave yourself wide open to these attacks.
In fact, the National Cyber Security Alliance reports that one in five small businesses have been victims of cybercrime in the last year – and that number is growing rapidly as more businesses utilize cloud computing and mobile devices and store more information online.
You can’t turn on the TV or read a newspaper without learning about the latest online data breach, and government fines and regulatory agencies are growing in number and severity. Because of all of this, it’s critical that you have these 7 security measures in place.
But I Have A Great IT Guy I Trust…
Many business owners are shocked when they get compromised because they BELIEVED their IT company or guy had it “handled.” However, there is a virtual army of thousands of hackers and very sophisticated crime rings that work around the clock to overcome known protections – and you can’t stop a brand-new threat that was invented yesterday with a security system that was designed six months to a year ago. It requires special expertise to stay on top of all of this, which is why many don’t.
To that end, here’s your quick7-step checklist. If YOUR company isn’t actually implementing ALL of these protocols – OR if you don’t know if you are –WHY NOT? What hasn’t your current IT company told you about all of this?
- The #1 Security Threat To ANY Business Is…You! Like it or not, almost all security breaches in business are due to an employee clicking, downloading or opening a file that's infected, either on a website or in an e-mail; once a hacker gains entry, they use that person's e-mail and/or access to infect all the other PCs on the network. Phishing e-mails (an e-mail cleverly designed to look like a legitimate e-mail from a website or vendor you trust)are still a very common occurrence – and spam filtering and antivirus cannot protect your network if an employee is clicking on and downloading the virus. That's why it's CRITICAL that you educate all of your employees in how to spot an infected e-mail or online scam.Cybercriminals are EXTREMELY clever and can dupe even sophisticated computer users. All it takes is one slip up, so constantly reminding and educating your employees is critical.On that same theme, the next precaution is implementing an Acceptable Use Policy. An AUP outlines how employees are permitted to use company-owned PCs, devices, software, Internet access and e-mail. We strongly recommend putting a policy in place that limits the websites employees can access with work devices and Internet connectivity. Further, you have to enforce your policy with content-filtering software and firewalls. We can easily set up permissions and rules that will regulate what websites your employees access and what they do online during company hours and with company-owned devices, giving certain users more "freedom" than others.Having this type of policy is particularly important if your employees are using their own personal devices and home computers to access company e-mail and data. With so many applications in the cloud, an employee can access a critical app from any device with a browser, which exposes you considerably.
If an employee is logging into critical company cloud apps through an infected or unprotected, unmonitored device, it can be a gateway for a hacker to enter YOUR network – which is why we don't recommend you allow employees to work remote or from home via their own personal devices.
Second, if that employee leaves, are you allowed to erase company data from their phone or personal laptop? If their phone is lost or stolen, are you permitted to remotely wipe the device – which would delete all of that employee's photos, videos, texts, etc. – to ensure YOUR clients' information isn't compromised?
Further, if the data in your organization is highly sensitive, such as patient records, credit card information, financial information and the like, you may not be legally permitted to allow employees to access it on devices that are not secured, but that doesn't mean an employee might not innocently "take work home." If it's a company-owned device, you need to detail what an employee can or cannot do with that device, including "rooting" or "jailbreaking" the device to circumvent security mechanisms you put in place. - Require STRONG Passwords and Passcodes To Lock Mobile Devices. Passwords should be at least 8 characters and contain lowercase and uppercase letters, symbols and at least one number. On a cell phone, requiring a passcode to be entered will go a long way toward preventing a stolen device from being compromised. Again, this can be ENFORCED by your network administrator so employees don't get lazy and choose easy-to-guess passwords, putting your organization at risk. Are they? If you and your employees are not being forced to do a password reset every 30-60 days, THEY ARE FAILING YOU.
- Keep Your Network and all Devices Patched and Up-To-Date DAILY. New vulnerabilities are frequently found in common software programs you are using, such as Adobe, Flash, Microsoft or QuickTime; therefore it's critical you patch and update your systems and applications as soon as patches become available. If you're under a managed IT plan, this can all be automated for you so you don't have to worry about an employee missing an important update.
- Have a Business-Class Backup BOTH On-Premise And In The Cloud. This can foil the most aggressive (and new) ransomware attacks, where a hacker locks up your files and holds them ransom until you pay a fee. If your files are backed up, you don't have to pay a crook to get them back. A good backup will also protect you against an employee accidentally (or intentionally!) deleting or overwriting files, and against natural disasters, fire, water damage, hardware failures and a host of other data-erasing disasters. Again, your backups should be AUTOMATED, TESTED and MONITORED; the worst time to test your backup is when you desperately need it to work!
- Don't allow employees to access company data with personal devices that aren't monitored and secured by YOUR IT department. The use of personal and mobile devices in the workplace is exploding. Thanks to the convenience of cloud computing, you and your employees can gain access to pretty much any type of company data remotely; all it takes is a known username and password. Employees are now even asking if they can bring their own personal devices to work (BYOD) and use their smartphone for just about everything.But this trend has DRASTICALLY increased the complexity of keeping a network – and your company data – secure. In fact, your biggest danger with cloud computing is not that your cloud provider or hosting company will get breached (although that remains a possibility); the biggest threat is that one of your employees accesses a critical cloud application via a personal device that is infected, thereby giving a hacker access to your data and cloud application.So if you ARE going to let employees use personal devices and home PCs, you need to make sure those devices are properly secured, monitored and maintained by a security professional. Further, do not allow employees to download unauthorized software or files. One of the fastest ways cybercriminals access networks is by duping unsuspecting users into willfully downloading malicious software by embedding it within downloadable files, games or other "innocent"-looking apps.But here's the rub: most employees won't want you monitoring and policing their personal devices; nor will they like that you'll wipe their device of all files if it's lost or stolen. But that's exactly what you'll need to do to protect your company. Our suggestion is that you allow employees to access work-related files, cloud applications and e-mail only via company-owned and monitored devices, and never allow employees to access these items on personal devices or public Wi-Fi.
- A Monitored Business-Class Firewall With Proper Updates. A firewall acts as the frontline defense against hackers blocking everything you haven't specifically allowed to enter (or leave) your computer network. But all firewalls need monitoring and maintenance, just like all devices on your network, or they are completely useless. This too should be done by your IT person or company as part of their regular, routine maintenance. HOWEVER, it's not uncommon for an IT guy to forget to turn on one or more of the intrusion detection and prevention features; often they are disabled to work on the firewall, but then never turned back on, making the device useless.
- Protect Your Bank Account. Did you know your COMPANY'S bank account doesn't enjoy the same protections as a personal bank account? For example, if a hacker takes money from your business account, the bank is NOT responsible for getting your money back. (Don't believe me? Go ask your bank what their policy is on refunding your money stolen from your account!) Many people think FDIC protects you from fraud; it doesn't. It protects you from bank insolvency, NOT fraud.So here are three things you can do to protect your bank account. First, set up e-mail alerts on your account so you are notified anytime money is withdrawn. The FASTER you catch fraudulent activity, the better your chances are of keeping your money. In most cases, fraudulent activity caught the DAY it happens can be stopped. If you discover it even 24 hours later, you may be out of luck. That's why it's critical that you monitor it daily and contact the bank IMMEDIATELY if you see any suspicious activity.Second, if you do online banking, dedicate ONE computer to that activity and never access social media sites, free e-mail accounts (like Hotmail) and other online games, news sites, etc., with that PC. Remove all bloatware (free programs like QuickTime, Adobe, etc.) and make sure that machine is monitored and maintained behind a strong firewall with up-to-date antivirus software.
And finally, contact your bank about removing the ability for wire transfers out of your account and shut down any debit cards associated with that account. All of these things will greatly improve the security of your accounts.
Are You REALLY Willing To Be Complacent About This?
Look, I know all of this appears to be a giant distraction and cost that interferes with REAL work. You and I both realize that implementing proper security protocols won’t win you the “employer of the year” award or deliver an ROI – in fact, we HOPE by doing OUR job, it never has to deliver one.
BUT if you foolishly choose to turn a blind eye and be arrogant, complacent or careless, cybercriminals WILL take advantage of you. You WILL pay the ransom…NOT YOUR IT COMPANY that was SUPPOSED TO PROTECT YOU. This tsunami of pain will land directly on YOUR desk to deal with, everyone pointing the blame at YOU. YOUR bank account. YOUR business. You will be faced with significant losses, costs and an emotional drain on you and your team as you deal with a breach.
Mark Twain Once Said, “Supposing Is Good, But KNOWING Is Better”
If you want to know for SURE that your current IT company (or IT person) is truly doing everything they can to secure your network and protect you from ransomware, bank fraud, stolen and lost data and all the other threats, problems and costs that come with a data breach, then you need to call us for a FREE Cyber Security Audit.
At no cost or obligation, we’ll send one of our security consultants and a senior, certified technician to your office to conduct a free Cyber Security Audit of your company’s overall network health to review and validate different data-loss and security loopholes, including small-print weasel clauses used by all third-party cloud vendors, giving them zero responsibility or liability for backing up and securing your data. We’ll also look for common places where security and backup get overlooked, such as mobile devices, laptops, tablets and home PCs. At the end of this free audit, you’ll know:
- Is your network really and truly secured against the most devious cybercriminals? And if not, what do you need to do (at a minimum) to protect yourself now?
- Is your data backup TRULY backing up ALL the important files and data you would never want to lose – and (more importantly) how FAST could you get your IT systems back online if hit with ransomware? We’ll reveal exactly how long it would take to restore your files (most people are shocked to learn it will take much longer than they anticipated).
- Are your employees freely using the Internet to access gambling sites and porn, to look for other jobs and waste time shopping, or to check personal e-mail and social media sites? You know some of this is going on right now, but do you know to what extent? Are they downloading illegal files (music and video) and exposing you, as happened with LabMD?
- Are you accidentally violating any PCI, HIPAA or other data-privacy laws? New laws are being put in place frequently, and it’s easy to violate one without even being aware; however, you’d still have to suffer the bad PR and fines if a breach happens and the investigation reveals YOU didn’t take necessary precautions – and ignorance is not an acceptable excuse that will get you out of a lawsuit.
- Is your firewall and antivirus configured properly and up-to-date? No security device is “set and forget.” It needs to be constantly monitored and updated – is yours? Is your IT company giving you the assurances that it is?
- Are your employees storing confidential and important information on unprotected cloud apps like Dropbox that are OUTSIDE of your backup? Could they walk off the job with a list of all your clients and go work for a competitor?
I know it’s natural to want to think, “We’ve got it covered.” Yet I can practically guarantee my team will find one or more ways your business is at serious risk for hacker attacks, data loss and extended downtime – I just see it all too often in the many businesses we’ve audited over the years.
Even if you have a trusted IT person or company who put your current network in place, it never hurts to get a third party to validate nothing was overlooked. I have no one to protect and no reason to conceal or gloss over anything we find. If you want the straight truth, I’ll report it to you.
You Are Under No Obligation To Do Or Buy Anything
I also want to be very clear that there are no expectations on our part for you to do or buy anything when you take us up on our Free Security And Backup Audit. As a matter of fact, I will give you my personal guarantee that you won't have to deal with a pushy, arrogant salesperson because I don't appreciate heavy sales pressure any more than you do.
Whether or not we're a right fit for you remains to be seen. If we are, we'll welcome the opportunity. But if not, we're still more than happy to give this free service to you.
You've spent a lifetime working hard to get where you are. You earned every penny and every client. Why risk losing it all? Get the facts and be certain your business, your reputation and your data are protected. Call us at (919) 800-0888 or you can e-mail me personally at [email protected].
Dedicated to serving you,
Joseph Martin
[email protected]
(919) 800-0888
To Request Your FREE Security & Backup Audit
Complete the request form at:
https://triangleitgroup.com/cyber-audit
- or -
Call us at (919) 800-0888
Here Are What A Few Of Our Clients Have Said:
Advanced Health & Rehabilitation Center Always take our concern seriously and immediately respond

We have been using Triangle IT Group for over 10 years. Prior to using them, we used various local computer companies and other people. They managed to get the job done and our systems working, but we were always oblivious when it came to maintenance care and monitoring. The inconsistencies in their service slowed down our production and reflected upon us negatively due to long wait times for service. This, in turn left us without the tools needed to properly care for our patients.
We rest easier at nights knowing that all of our important and private patient information is safe, secure and there is someone on the other end monitoring and ready to act if ever needed. The implementation of our new office server took us light years ahead of the competition and has increased our ability to service a great number of patients daily. With peace of mind and confidence that our systems are working appropriately, we can put our focus on our main priority of patient care.
He has assisted us with so many aspects of the business. From computer repair, to software advise and installs, we are never let down. I always enjoy their knowledgeable team visiting and talking with them over the phone. They are always willing to go the extra mile and explain the process of things as well as teach me and our staff ways to help avoid issues in the future. That alone is priceless.
All our issues seem to take high priority with Triangle IT Group. While I know they have several high-profile customers, they always take our concern seriously and immediately respond. We could not have a better or more dependable company to work with for all our IT needs.
I would tell people, and I have told them, that there is no other company to call in Eastern NC but Triangle IT Group. I believe that a good company stands behind its product, treats others with respect, does as it says it's going to, and does not take advantage financially of those that may not know better, Triangle IT Group is certainly a wonderful representation of all those qualities and more..
Dr. Brian Kean,
President of Advanced Health & Rehabilitation Center
The Robert Taylor Group Good folks that do a great job for a fair price

I have been using Triangle IT Group for several years. The company we used before was very spotty but now that we use Triangle IT Group our service is very good.
Whenever we have an issue it is very easy to get up with them to handle our problem and they handle it on a very timely bases. They are very helpful about suggesting new ideas to help us out. They are good folks that do a great job for a fair price.
Ken Lang,
President of The Robert Taylor Group
ACF Insurance Services, Inc. They are so nice to deal with, so it is a no brainer for us

I have been using Triangle IT Group for 4 years. The provider we had before was good, but now that we use Triangle IT Group it’s even better than before! Whenever we have any issues or emergencies it is very easy to get assistance and the issues get resolved very quickly. I am very glad I switched too!
Triangle IT Group helps us stay up with technology and changes so that we have secure and reliable systems. They are so nice to deal with, so it is a no brainer for us as to why we chose them. Plus, I would refer my best friend in a second to use Triangle IT Group.
Matt Alala,
President of ACF Insurance Services, Inc.
The Appraisal Advantage Switching to Triangle IT Group was one of the best business decisions

We have been using Triangle IT Group for 10+ years. The service from other IT companies was erratic and undependable at best. However, now our service is quick, reliable, and personable. Whenever I have an IT issue, help is just a phone call away. All of my IT issues get resolved quickly, which is very important to minimize my office downtime.
Switching to Triangle IT Group was one of the best business decisions that I have made. They give me the peace of mind in knowing that if I do have an IT issue, it will be resolved within a very short period of time and my office will be back up and running.
I have recommended Triangle IT Group to several of my friends for their businesses and will continue to do so!
Ashley Barker,
Owner of The Appraisal Advantage
Car Mart of Greenville Things are fixed right the first time

My name is Steven White and I work at Car Mart of Greenville. I am the president, buyer, and controller for the company. We have been using Triangle IT Group for 8 years. The company we used before was sloppy and slow. Now that we are with Triangle IT Group, they are punctual, things are fixed right the first time and they have very fair pricing!
When we have issues and have to call, it is easy to get help and they resolve the problem quickly. I would say that these folks are polite, easy to get along with and got our computers running faster. I would tell any and every one to call Triangle IT Group.
Steven White,
Car Mart of Greenville
Textbook Brokers We now have a much more reliable network
We have been using Triangle IT Group for around 8 years. The other companies that we used in the past were unreliable. These guys are knowledgeable, competitively priced and fast. When we have issues, they are very easy to get up with and come out quickly to handle our problem. They also get things resolved very quickly!
I am definitely glad we switched to Triangle IT Group. We now have a much more reliable network and I tell everyone that ask to use the Triangle IT Group.
Jeremy Cucinella,
Regional Manager for Textbook Brokers
Gregory K. James, P.A. Attorneys at Law We are very glad that we switched to Triangle IT Group

We have been using Triangle IT Group for over 5 years. Before, we were using an independent person to take care of our computers and servers. Now that we use Triangle IT Group our IT service has been excellent. If we do have issues, we have no problems getting our issues handled quickly.
We are very glad that we switched to Triangle IT Group. We now we have a peace of mind, plus they are very understanding and patient. I would tell my best friend to call the Triangle IT Group if you want the best.
Greg James,
Owner Gregory K. James, P.A. Attorneys at Law
Dimensions Professional Search I would not hesitate to recommend Triangle IT Group

I have been using Triangle IT Group for around 10 years. The company I used before was adequate, but very overpriced. Now that I use Triangle IT Group, they have helped us change from a local network environment to a cloud based network environment and has managed our IT infrastructure since then.
When we do have a problem, it is very easy to get in touch with Triangle IT Group and they can check the problem remotely or come to our site if necessary. They have any problems resolved very quickly. I am definitely glad we switchedand I would not hesitate to recommend them as an IT vendor of choice
Jeff Sutherland,
Principal Partner at Dimensions Professional Search
